The Meaning of AWS Identity and Access Management (IAM)?
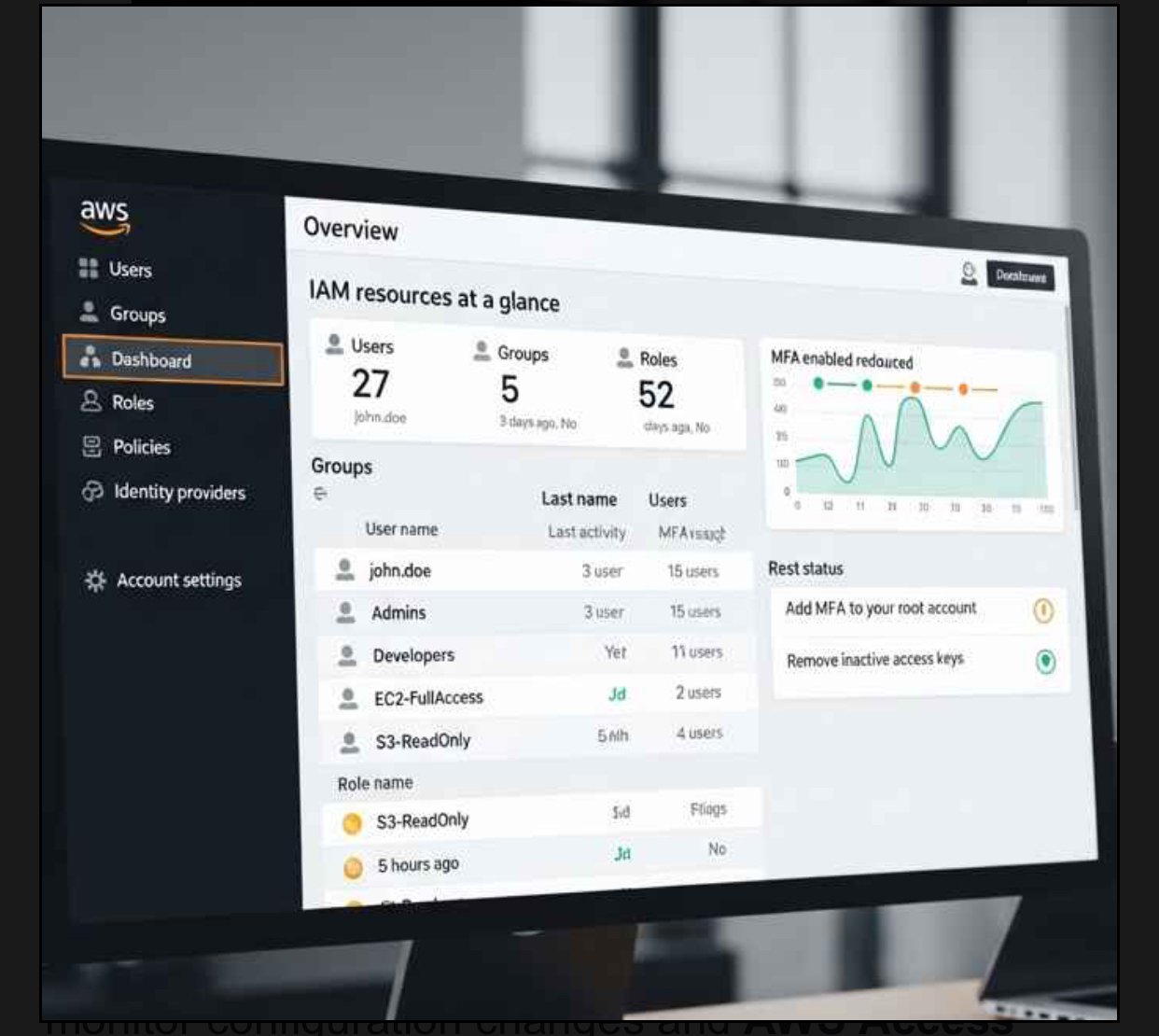
When you Think of AWS IAM as the bouncer at an exclusive nightclub, but for your cloud resources. It’s Amazon’s free service that controls who can access what in your AWS environment. Unlike a simple username-password system, IAM operates on the principle of “least privilege”—giving users only the minimum permissions they need to do their job.
The beauty of IAM lies in its granularity. You can specify that Sarah from marketing can only view S3 buckets on Tuesdays between 9 AM and 5 PM, while Bob from development can create EC2 instances but only in the US-East region. This level of control might seem excessive, but it’s exactly what prevents those midnight security incident calls.
AWS CloudTrail logs every IAM action, creating a detailed audit trail. Combine this with AWS Config to monitor configuration changes and AWS Access Analyzer to identify unused permissions or potential security risks.
Set up alerts for suspicious activities like:
- Failed login attempts from unusual locations
- Creation of new administrative users
- Changes to critical policies
- Unusual API usage patterns
Common IAM Pitfalls to Avoid
The biggest mistake I see organizations make is starting with overly permissive policies and gradually restricting access. This backwards approach creates security gaps and frustrated users when permissions suddenly disappear.
Instead, start restrictive and gradually add permissions as needed. Yes, you’ll get more “permission denied” tickets initially, but you’ll sleep better knowing your environment is secure by default.
Another common trap is neglecting credential rotation. AWS access keys should be rotated regularly, and unused credentials should be deleted promptly. Set up automated reports to identify stale access keys and remove them.
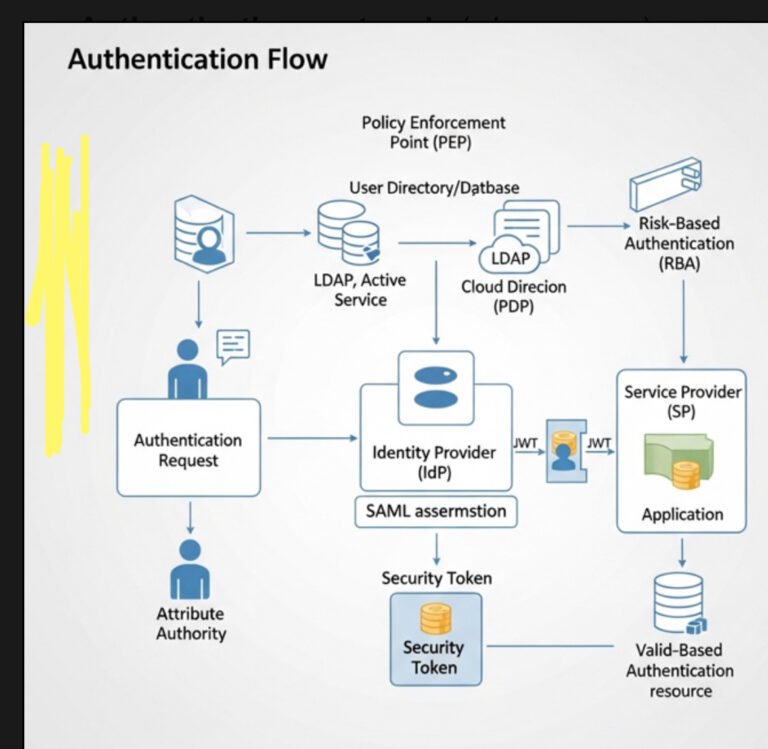
The Future of IAM: Attribute-Based Access Control
AWS is evolving toward attribute-based access control (ABAC), where access decisions are based on attributes like department, project, or data classification rather than static roles. This approach provides more flexibility and reduces policy sprawl as organizations scale.
Conclusion
Identity and Access Management IAM AWS isn’t just a technical requirement—it’s your first line of defense against security breaches, compliance violations, and unexpected costs. By implementing proper IAM controls, you’re not just checking a compliance box; you’re building a foundation for secure, scalable cloud operations.
Start with the basics: create individual users, group them logically, enable MFA, and follow the principle of least privilege. As your expertise grows, explore advanced features like cross-account roles, automation tools, and centralized identity management.
The cloud security landscape changes rapidly, but solid IAM fundamentals remain constant. Invest the time to get IAM right from the beginning, and you’ll avoid the painful (and expensive) lessons that come from learning it the hard way.
What’s your biggest IAM challenge? Share your experiences in the comments below, or bookmark this guide for your next AWS project. Your future self will thank you.
Frequently Asked Questions
1. What’s the difference between IAM users and IAM roles?
IAM users are permanent identities with long-term credentials, while IAM roles provide temporary credentials that can be assumed by users, services, or applications. Use users for people and roles for services or temporary access needs.
2. How often should I rotate AWS access keys?
AWS recommends rotating access keys every 90 days. However, the best practice is to use IAM roles instead of access keys whenever possible, as roles provide automatically rotating temporary credentials.
3. Can I use my existing Active Directory with AWS IAM?
Yes, through AWS IAM Identity Center or AWS Directory Service, you can federate your existing Active Directory with AWS, allowing users to access AWS resources using their corporate credentials.
4. What happens if I accidentally lock myself out of my AWS account?
If you’re locked out due to IAM policy restrictions, you can use the AWS account root user to regain access. This is why protecting and rarely using the root user credentials is crucial—they’re your emergency access method.
5. Is AWS IAM free to use?
Yes, AWS IAM is a free service. You only pay for the AWS resources that your users access through IAM. There are no additional charges for IAM users, groups, roles, or policies.