Last Tuesday morning, I received a panicked Slack message from a CTO friend: “We just found 500+ misconfigured S3 buckets exposed to the internet. How did we miss this?” Unfortunately, this scenario plays out daily across organizations worldwide. With companies managing resources across AWS, Azure, and Google Cloud, keeping track of security configurations has become a nightmare.
This is exactly why CSPM cloud security has evolved from a “nice-to-have” into an absolute necessity. If you’re managing cloud infrastructure—whether you’re a security professional, DevOps engineer, or business leader—understanding Cloud Security Posture Management could save your organization from the next major data breach.
In this comprehensive guide, you’ll discover what CSPM really means, how it works in practice, the top tools worth your investment, and actionable strategies to implement cloud security posture management effectively. By the end, you’ll have a clear roadmap for securing your cloud environment against today’s most pressing threats.
What Is CSPM Cloud Security?
Cloud Security Posture Management (CSPM) is your organization’s security watchdog for cloud environments. Think of it as a continuous auditor that never sleeps, constantly scanning your cloud infrastructure to identify misconfigurations, compliance violations, and security risks.
Here’s what makes CSPM different from traditional security tools: instead of waiting for attacks to happen, it prevents them by ensuring your cloud resources are properly configured from day one. It’s like having a security expert review every single cloud resource you deploy, 24/7.
Why Traditional Security Falls Short in the Cloud
The cloud operates fundamentally differently than on-premises infrastructure. When you’re managing hundreds or thousands of resources across multiple cloud providers, manual security reviews become impossible. Consider this:
- A typical enterprise manages over 1,000 cloud resources
- New resources are deployed every few minutes
- Each resource has dozens of configuration options
- One wrong setting can expose sensitive data globally
This is where cloud security posture management becomes invaluable—it automates the impossible task of keeping everything secure.
How CSPM Works: The Technical Magic Behind the Scenes
Understanding how CSPM tools operate helps you appreciate their value. Here’s the step-by-step process:
1. Discovery and Inventory
CSPM solutions automatically discover all cloud resources across your infrastructure. They map everything from virtual machines to storage buckets, databases to network configurations.
2. Configuration Assessment
Every discovered resource gets compared against security best practices and compliance standards. The tool checks hundreds of configuration settings per resource.
3. Risk Analysis and Prioritization
Not all security issues are equal. CSPM platforms use sophisticated algorithms to prioritize risks based on:
- Exposure level (internet-facing vs. internal)
- Data sensitivity
- Potential attack paths
- Compliance requirements
4. Automated Remediation
Advanced CSPM solutions can automatically fix certain misconfigurations. For example, they might automatically enable encryption on a storage bucket or adjust network access controls.
Top CSPM Cloud Security Tools for 2025
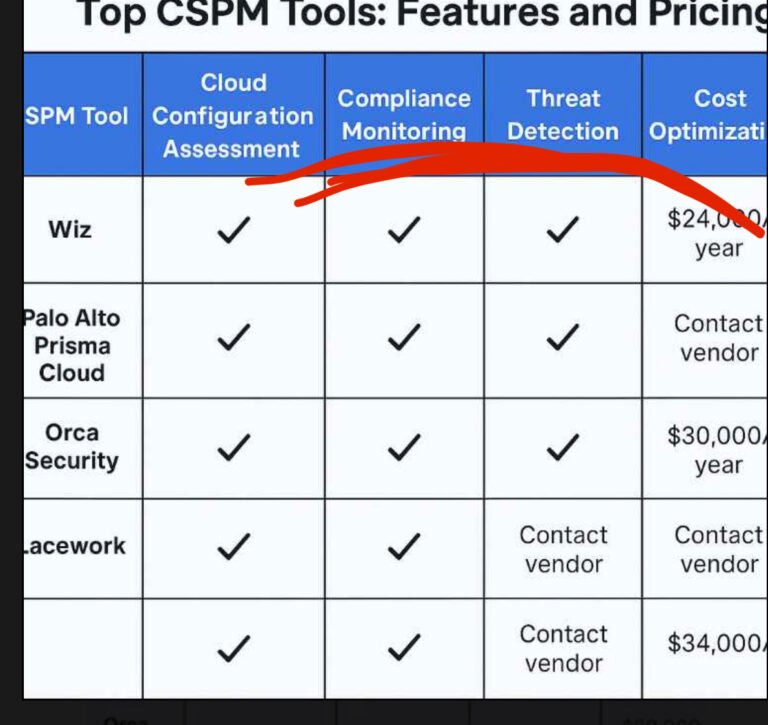
Based on extensive market research and real-world testing, here are the leading CSPM cloud security tools:
| CSPM Solution | Best For | Key Strengths | Pricing Model |
|---|---|---|---|
| Wiz CSPM | Large enterprises | Agentless scanning, risk prioritization | Per-workload |
| Palo Alto Prisma Cloud | Comprehensive security | Full CNAPP capabilities, strong automation | Enterprise licensing |
| Orca Security | Mid-market companies | SideScanning technology, easy deployment | Resource-based |
| Microsoft Defender for Cloud | Azure-heavy environments | Native integration, cost-effective | Per-resource |
| AccuKnox CNAPP | DevSecOps teams | Zero trust runtime, attack path analysis | Subscription-based |
Deep Dive: Why These Tools Stand Out
Wiz has revolutionized agentless cloud security posture management by scanning cloud environments without installing any software. Their security graph technology creates a comprehensive map of your entire cloud infrastructure, making it easy to understand complex attack paths.
Palo Alto Prisma Cloud excels at automated cloud compliance monitoring, with pre-built policies for major compliance frameworks. Their machine learning capabilities continuously improve threat detection accuracy.